Overcoming IT security challenges
Let your IT infrastructure and its security grow step by step with your business. It seems obvious but many companies fail to do so for various reasons.
A too-small IT team that has other focuses, no or low budgets for IT, "we have other priorities as a company". These are all excuses that both we and your IT team have heard before. A Security Audit wipes them all away.

How does our Security audit work?
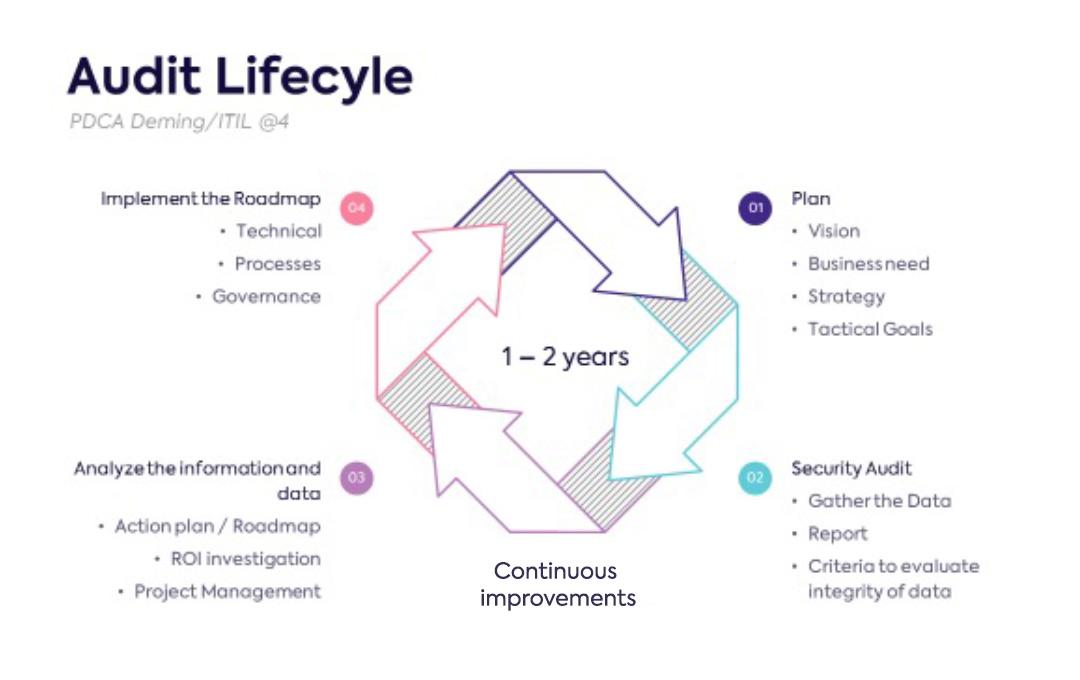
A well established security audit is performed according to a number of agreed upon business and IT standards (more on that here).
In order to provide your company with a detailed security roadmap according to your business needs and budgets, we first examine the current status of your security posture on 4 different levels.
Our approach: The 4 investigated security levels
Organizational
We match security to your business vision, your people, your current IT infrastructure and your processes around information sharing and protection.
Physical security
Think about the physical components of your IT security such as access to your offices or where your systems are located. What if there is a fire? What about security awareness of employees? Etc...
Network architecture
How is your network structured and how can you make it more performant, more reliable and where should redundancy be added?
System hardening
The compliance of how systems and software are configured is evaluated. A deep-dive into updates, patches, etc.
Get in touch
Security Audit step by step guide
During a kick-off meeting, we match your needs in terms of IT infrastructure and security with your business vision. We do this through an in-depth conversation with different stakeholders and with the help of a well-prepared questionnaire. This way we can better advise you in achieving your tactical goals at a later stage and design the security roadmap that suits you best.
During the security audit, we work according to the agreed principles using your chosen Security audit pack.
We do a thorough analysis of your IT infrastructure in terms of market best practices, business standards or legal protocols in terms of certification. This according to an agreed framework and without harming the integrity of your company.
Based on the previous findings, we build an advanced report that is linked to your previously described needs. This way, the security audit provides an ideal mix of quick-wins, mid-long term and long term implementations. In this way, you can let your IT infrastructure grow organically with your company without growing pains. You will receive an action plan from us that includes a detailed ROI by topic.
Our pragmatic approach will ensure that project management and change management are top priorities. Our auditors think along with you and the needs of your company.
If you wish, your IT team will be continuously involved in the security audit so that they too can more easily tackle the necessary action points from the Roadmap at a later stage.
In order not to leave you to your fate after the audit, our experts will also guide you in the more technical part of the security roadmap, the implementation.
Our positioning as a best of breed IT provider allows us to offer you different solutions. We also look at the optimization of processes and possible governance actions.
A security audit is best performed sporadically, we recommend annually or every 2 years. This is because your organization, systems and people are constantly changing. The changing situation also affects your security posture.
The ideal security Roadmap, we create it together.
Thanks to our plug-and-play security audit service, you have a greater say in the outcome. The different modules allow you to determine both the depth of the analysis and the level of involvement of your IT team.
(Since it's about your company and its future, we strongly recommend some engagement from your side).
Our security audit packs - choose the pack that suits you best
Want to know more about our offering and prices of a security audit?
*Feel free to put together your ideal Security audit or contact our experts to guide you.





