Why rely on a penetration testing service?
Is my company data sufficiently protected? That's the question a lot of SMBs and larger companies ask themselves. Our penetration testing service provides an answer to that question.
Every organization processes a lot of data every day. As a result of digitalization, we do this more and more online. This data - whether it is critical, unimportant or strictly confidential - is a target for cybercriminals.
Know your weaknesses
As a company, you've probably already taken a number of measures to protect your (most sensitive) data. But are those cybersecurity measures you've taken sufficient?
Pentest-as-a-Service
Through our penetration testing service we let ethical hackers loose on your company. They put themselves in the shoes of real cybercriminals and apply all the techniques that real hackers would use to get hold of your data.
Security posture analysis
Our penetration testing service forms an important part of your security posture analysis and is the most truthful way to evaluate whether or not your data is sufficiently secure. This analysis not only gives you insights but also a roadmap with solutions.
This was our first penetration test. We had no idea what we were getting into.
Fortunately, we were quickly reassured by the flexibility, attentiveness and professionalism of the Easi team.
Grégory Sacré - Project Set-up Manager at S-Clinica

Are you ready for the test?
Is such a penetration testing service even legal?
Of course! A penetration test is always preceded by determining the scope and is performed by our certified Ethical hackers.
As a company, you indicate what you want to examine, after which our penetration testing service will provide you with a crystal-clear insight into the weak points of your organization, application(s), IT networks, you name it.

What does the penetration testing service cover?
Network pen test
(Web) application pen test
Cloud pen test
Physical pen test
This is one of the most common penetration tests, especially when your business network or Wi-Fi network is a critical factor in the day-to-day operation of your business. The goal is to identify both the most visible vulnerabilities, and underlying security shortcomings of your network infrastructure by hacking servers, firewalls, switches, routers, printers, etc., before they can be exploited by cybercriminals.
Our penetration testing service provides both external and internal network penetration testing. In the first case, we try to break through your firewalls from the outside. In an internal penetration test, the goal is to mimic the role of a malicious insider - an (ex-)employee, partner, or suchlike with malicious intent. In many cases, this is a test that is best repeated annually.
This type of penetration testing is much more detailed, focused and therefore more complex. In a web application pen test, all web based applications, browsers and their components such as ActiveX, Plugins, Silverlights, etc. are taken into consideration in the scope. In short, all endpoints that the user comes into contact with are tested.
The pen test is designed to find all potentially vulnerable code that an attacker could use to take over the application. We look for: Broken Access Control, Cryptographic Failures, Injection Flaws, Insecure Design, faulty configurations, ...
You don't own the infrastructure, platform, or software, you just use your cloud as a service. Still, there is shared responsibility in the event of a data breach. That's why performing a cloud penetration test is always a good idea. However, this comes with a number of legal and technical challenges.
A cloud penetration test is intended to provide companies with a better understanding of their security in their cloud setup. It looks at the security of cloud-specific configurations, passwords for cloud systems, cloud applications and encryption, APIs, databases, storage access in the form of weak passwords, etc.
In cybersecurity, physical barriers such as access to company sites or cameras, etc., are often the most underestimated vulnerability. Our pentesters will attempt to penetrate your company site to gain access to, for example, your company network, server room, or company devices.
During the penetration testing service, we evaluate vulnerabilities such as social engineering, shoulder-surfing, or badge mimicry.
Whether you want to perform the penetration test in the context of an ISO certification, before the launch of a (web) application, or maybe just because a possible ransomware attack frightens you,
our pentesters are ruthless, but ethical. 😉
These companies already trust us
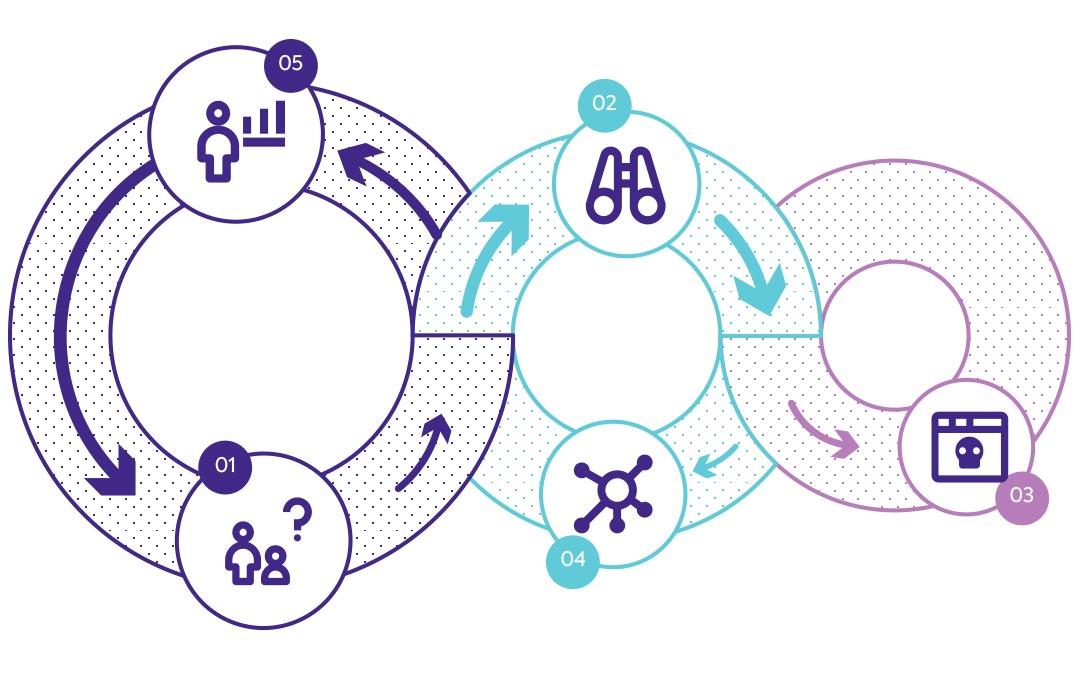
How does the penetration testing service work?
You can read exactly how our penetration testing service works here or in the short summary below.
We always start unnoticed, thanks to a thorough scanning of both your online and physical vulnerabilities. This can be done from the outside, but also from the inside!
Our penetration testing service can proceed according to three pen testing principles, depending on your choice:
White-box pen test
White box - or glass box testing: we get as much information as possible about your company, system or application in advance. This mainly involves looking at the logical structure of, for example code, algorithms or configurations and testing the boundaries of them.
Grey-box pen test
In doing so, we have certain knowledge about your internal processes, code or security posture. Typically, this penetration testing service is performed after a real attack that may or may not have succeeded in hacking your systems. In this, we dig deeper to overcome the boundaries between internal software and physical factors.
Black-box pen test
In the black-box penetration testing service, we have no prior knowledge of internal processes or code. We proceed just like cybercriminals who want to exploit your vulnerabilities from the outside. It is the most appealing test for our ethical hackers because they can often also perform a physical pen test, in which they try to enter your buildings unnoticed and try to capture sensitive information.
What after the penetration testing service?
A detailed report will be provided after the test. This report contains the weaknesses we were able to exploit / "get around". We will prepare a detailed report in which you can assess all your weaknesses against your security posture.
Our ethical hackers not only provide you with a detailed report, but also think along with you according to your company needs. They will provide you with a concrete plan for the future. A plan that takes into account internal know-how and budget. This gives you a step-by-step plan that you can tackle yourself or with a little help form us.

Recurring Penetration testing service
Finally, Easi would also like to point out weaknesses that we were unable to exploit during penetration testing, but where unauthorized access can be gained over time. This is important because the timing of our testing is limited, but malicious hackers have all the time in the world! So performing a pen test on a regular basis is not an unnecessary luxury.